Analytics & Intelligence Application Security AppSec Cloud Security Cloud Security Cybersecurity Data Privacy Data Security Deep Fake and Other Social Engineering Tactics DevOps DevSecOps Editorial Calendar Endpoint Featured Governance, Risk & Compliance Humor Identity & Access Identity and Access Management Incident Response Industry Spotlight Malware Most Read This Week Network Security News Popular Post Ransomware Securing Open Source Securing the Cloud Securing the Edge Security at the Edge Security Awareness Security Boulevard (Original) Security Operations Social Engineering Software Supply Chain Security Spotlight Threat Intelligence Threats & Breaches Vulnerabilities Zero-Trust
Topic Spotlight
168极速赛车官网开奖历史、历史记录查询在线官方 and Intelligence
Analytics & Intelligence Application Security Cloud Security Cybersecurity Featured Governance, Risk & Compliance Identity & Access Network Security News Security Boulevard (Original) Social - Facebook Social Engineering Spotlight Threat Intelligence Threats & Breaches Vulnerabilities
Survey Sees Zero-Trust Transition Gaining Momentum
Incident Response
Analytics & Intelligence API Security AppSec Cloud Security Cloud Security Cybersecurity Data Privacy Data Security DevOps DevSecOps Editorial Calendar Featured Governance, Risk & Compliance Humor Identity & Access Identity and Access Management Incident Response Industry Spotlight Insider Threats IOT IoT & ICS Security Most Read This Week Network Security News Popular Post Securing the Cloud Securing the Edge Security at the Edge Security Awareness Security Boulevard (Original) Spotlight Threat Intelligence Threats & Breaches Vulnerabilities Zero-Trust
Cisco Zero-Day: As Bad as it Gets — and No Fix 4 Weeks in
AI and Machine Learning in Security AI and ML in Security Analytics & Intelligence Application Security AppSec Cloud Security Cloud Security Cyberlaw Cybersecurity Deep Fake and Other Social Engineering Tactics DevOps DevSecOps Editorial Calendar Featured Governance, Risk & Compliance Humor Incident Response Industry Spotlight Insider Threats Mobile Security Most Read This Week Network Security News Popular Post Regulatory Compliance Securing the Cloud Security Awareness Security Boulevard (Original) Security Operations Social - Facebook Social Engineering Spotlight Threat Intelligence
Elon’s CSAM FAIL: Twitter Fined by Australian Govt.
IoT & ICS Security
Analytics & Intelligence Application Security AppSec Cloud Security Cloud Security Cyberlaw Cybersecurity Data Privacy Deep Fake and Other Social Engineering Tactics DevSecOps Editorial Calendar Endpoint Featured Governance, Risk & Compliance Humor Identity & Access Identity and Access Management Incident Response Industry Spotlight Insider Threats IOT IoT & ICS Security Mobile Security Most Read This Week Network Security News Popular Post Regulatory Compliance Securing the Cloud Securing the Edge Security at the Edge Security Awareness Security Boulevard (Original) Social Engineering Spotlight Threat Intelligence Threats & Breaches Zero-Trust
Stalking: Fear of Apple AirTag ‘Explodes’ — Lawsuit Momentum Grows
Industry Spotlight
Analytics & Intelligence Application Security AppSec Cloud Security Cloud Security Cybersecurity Data Privacy Data Security Deep Fake and Other Social Engineering Tactics DevOps DevSecOps Editorial Calendar Endpoint Featured Governance, Risk & Compliance Humor Identity & Access Identity and Access Management Incident Response Industry Spotlight Malware Most Read This Week Network Security News Popular Post Ransomware Securing Open Source Securing the Cloud Securing the Edge Security at the Edge Security Awareness Security Boulevard (Original) Security Operations Social Engineering Software Supply Chain Security Spotlight Threat Intelligence Threats & Breaches Vulnerabilities Zero-Trust
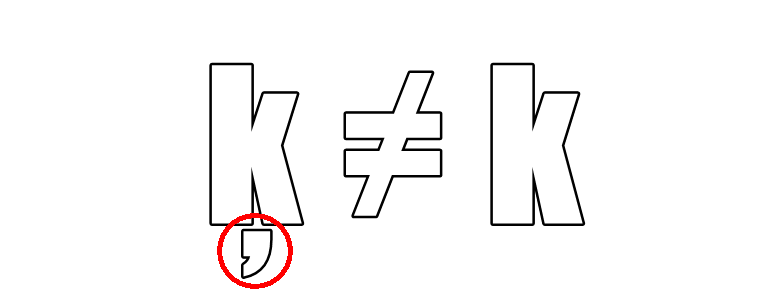
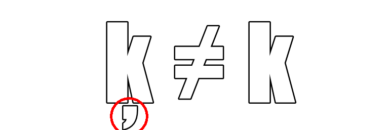
KeePass Malicious Ads: Google Goof Permits Punycode Attacks Again
Mote below k: Not only malvertising, but also “verified by Google.”


Analytics & Intelligence API Security AppSec Cloud Security Cloud Security Cybersecurity Data Privacy Data Security DevOps DevSecOps Editorial Calendar Featured Governance, Risk & Compliance Humor Identity & Access Identity and Access Management Incident Response Industry Spotlight Insider Threats IOT IoT & ICS Security Most Read This Week Network Security News Popular Post Securing the Cloud Securing the Edge Security at the Edge Security Awareness Security Boulevard (Original) Spotlight Threat Intelligence Threats & Breaches Vulnerabilities Zero-Trust
Cisco Zero-Day: As Bad as it Gets — and No Fix 4 Weeks in
Click here for Industry spotlight inclusion guidelines
The Industry Spotlight Section of Security Boulevard is the place where tools and service providers in the security field contribute to the community discussion with original content. While there are vendor blogs in the Security Bloggers Network, original content from these vendors are featured here. The articles here must meet several criteria to be published:
- * Must be original when published
- * Must be vendor neutral
- * Must be transparent as to authorship
- * Must be of value to the community