Incident Response

KeePass Malicious Ads: Google Goof Permits Punycode Attacks Again
Richi Jennings | | IDN, IDN homograph phishing, internationalized domain names, KeePass, Punycode, SB Blogwatch
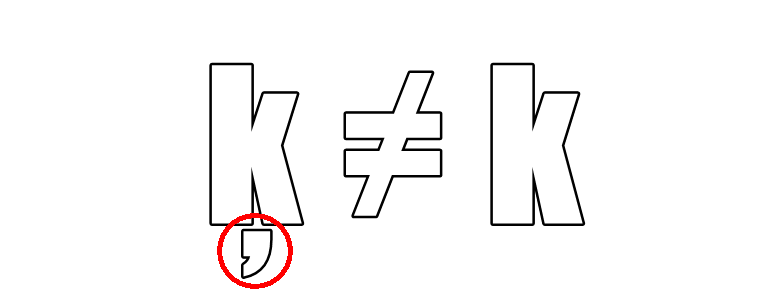
Mote below k: Not only malvertising, but also “verified by Google.” ...
Security Boulevard

Bi-Directional Sync with Microsoft Sentinel and Smart SOAR
Pierre Noujeim | | Bi-Directional Sync, Co-managed SIEM Services, incident management, Incident Response, Incident_Response, Microsoft Sentinel, MSSP, MSSPs, multi-tenancy, SIEM, Smart SOAR, SOAR, Workflow Optimization
Managed security service providers (MSSPs) and organizations that oversee multiple security teams will often have to manage multiple tenants of Microsoft Sentinel. In this situation, it’s inefficient and overwhelming to switch between ...

Survey Surfaces High Levels of Burnout Among Cybersecurity Professionals
The majority of cybersecurity pros are experiencing some level of burnout, with more than half reporting they are likely to switch jobs next year ...
Security Boulevard

Cisco Zero-Day: As Bad as it Gets — and No Fix 4 Weeks in
Richi Jennings | | 0-day, 0-day exploits, 0-day vulnerability, 0day, cisco, Cisco IOS XE, CVE-2023-20198, SB Blogwatch, Zero Day Attacks, zero-day, Zero-Day Bug, Zero-day Exploit, zero-day exploits, zero-day flaw, zero-day flaws, zero-day threat, zero-day vulnerabilities, Zero-day Vulnerability, zero-days, zeroday, zerodayvulnerabilities
Keeping us in suspense—It doesn’t get worse than this: CVE-2023-20198 is CVSS=10 ...
Security Boulevard

Elon’s CSAM FAIL: Twitter Fined by Australian Govt.
Richi Jennings | | Australia, Australian Government, Child Abuse, child exploitation, Child Online Safety, child porn, child pornography, Child protection, Child Safety, child security online, child sexual exploitation, childpornography, CSAM, Digital Trust and Safety, Elon Musk, elon musk twitter, eSafety Commission, grooming, Julie Inman Grant, Linda Yaccarino, SB Blogwatch, trust and safety, Twitter, X
Straya strikes back: Musk’s mob declines to answer questions, breaking law dunundah ...
Security Boulevard

NSA Releases EliteWolf GitHub Repository for Securing OT Environments
The National Security Agency released a code repository in GitHub to make it easier for critical infrastructure organizations and similar entities to better identify and detect potentially malicious activities in their operational ...
Security Boulevard

Stalking: Fear of Apple AirTag ‘Explodes’ — Lawsuit Momentum Grows
Richi Jennings | | AirTag, AirTags, Apple, Apple AirTag, cyberstalking, Digital Stalking, Find My iPhone, SB Blogwatch, Stalkerware, Stalking, Stalkware, Tracker Detect, trackers
This is why we can’t have nice things: 38 victims of Apple’s “negligence” named in amended class action ...
Security Boulevard

Why Some Organizations Become Victims of Repeat Ransomware Attacks
It’s not a matter of if, but when an organization falls victim to a cyberattack. Despite increased awareness of ransomware’s risks and despite organizations’ efforts to increase security measures, attackers seem to ...
Security Boulevard

Survey Sees Cyberattacks Impacting Primary Health Care Services
A Proofpoint survey found the majority of health care organizations experienced an average of 40 attacks in the past 12 months ...
Security Boulevard
![[Darktrace + D3 Smart SOAR ] Automate, Detect & Respond](png/lazy_image.png)
Why Smart SOAR is the Best SOAR for Darktrace
Pierre Noujeim | | AI-Driven Security, Cybersecurity, Darktrace, Device Analysis, Incident Response, Integration Guide, Post-Incident Analysis, Real-Time Response, Smart SOAR, SOAR, threat detection, Threat Hunting
The need for integrated cybersecurity solutions has never been more pressing. With the growing complexity of cyber threats, having siloed security tools is no longer an option. This is where the synergy ...