Cisco Zero-Day: As Bad as it Gets — and No Fix 4 Weeks in
Keeping us in suspense—It doesn’t get worse than this: CVE-2023-20198 is CVSS=10 ... Read More

RomCom Malware Group Targets EU Gender Equality Summit
A hacker group that continues to extend its reach from financially motivated attacks into cyber-espionage this summer targeted attendees of a gender equality conference with a pared-down version of the RomCom remote access trojan (RAT). Void Rabisu – also known as Tropical Scorpius, Storm-0978, and UNC2596 – in August leveraged ... Read More

Elon’s CSAM FAIL: Twitter Fined by Australian Govt.
Straya strikes back: Musk’s mob declines to answer questions, breaking law dunundah ... Read More

Microsoft Launches an AI Bug Bounty Program
As Microsoft aggressively integrates AI into its broad portfolio of products and services, the IT giant now is looking for help to ensure they are free of vulnerabilities. The company this month unveiled a new bug bounty program that will pay between $2,000 and $15,000 for flaws found in its ... Read More

NSA Releases EliteWolf GitHub Repository for Securing OT Environments
The National Security Agency released a code repository in GitHub to make it easier for critical infrastructure organizations and similar entities to better identify and detect potentially malicious activities in their operational technology (OT) environments. The agency announced this week that it released the repository for OT Intrusion Detection Signatures ... Read More

Stalking: Fear of Apple AirTag ‘Explodes’ — Lawsuit Momentum Grows
This is why we can’t have nice things: 38 victims of Apple’s “negligence” named in amended class action ... Read More

Hackers Still Abusing LinkedIn Smart Links in Phishing Attacks
Email security firm Cofense in 2022 uncovered a phishing campaign that abused LinkedIn’s Smart Links feature to redirect unsuspecting victims to malicious websites, another example of bad actors using a trusted source to bypass security measures and reach users. At the time, hackers were using the phishing campaign to convince ... Read More

Survey Sees Cyberattacks Impacting Primary Health Care Services
A Proofpoint survey found the majority of health care organizations experienced an average of 40 attacks in the past 12 months ... Read More

Google Pushes ‘Passkeys’ Plan — but it’s Too Soon for Mass Rollout
FIDO FAIL: “Killing passwords” is a worthy goal—but is coercion the best way? ... Read More

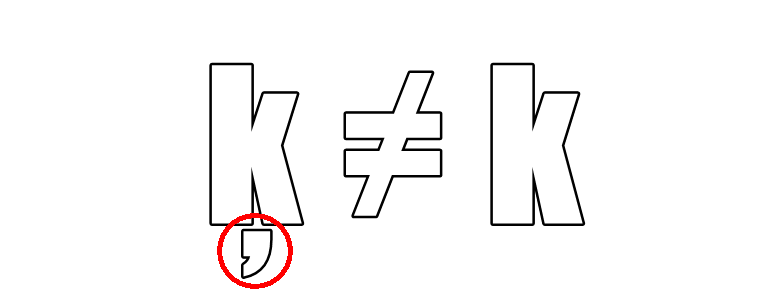
Heads Up: Patch for ‘Worst Curl Security Flaw’ Coming This Week
Developers who use the popular curl open-source data transfer tool will be able to patch two vulnerabilities in the software on October 11, one of which the lead developer called the “worst curl security flaw in a long time.” Daniel Stenberg, who also is the original author of curl, earlier ... Read More